Cybersecurity is a business imperative today. As risks rise, so does the value of certification for security professionals. A Certified Information Systems Security Professional (CISSP) is the gold standard today. While many organizations value the certification, many more require it. CISSP is often the baseline for career progression in large organizations, including the federal government. For the Department of Defense, DoD Directive 8570.01-M includes CISSP as one of the approved certifications on all Level 3 position categories.
As a CISSP, you are in a great position to maximize career earnings and relevance. This designation communicates your experience and understanding of all aspects of cybersecurity.
Is it for you? The answer is “yes” if you:
- Have at least 5 years of relevant experience
- Have a role related to Governance and/or Risk Assessment
- Plan to find a new position soon
- Seek a salary negotiation at your current job
- Want to enhance your resume
- Aspire to a management role
Read on to learn more about the CISSP NIST list to become certified and raise your value as a cyber professional.
What Is CISSP?
The Certified Information Systems Security Professional (CISSP) is an information security certification for security analysts. Created by the International Information Systems Security Certification Consortium (ISC2), the certification helps ensure professionals in information security have standardized knowledge of the field. For those who hold the coveted designation as a CISSP, it can mean significant potential to do, and earn, more in your IT career.
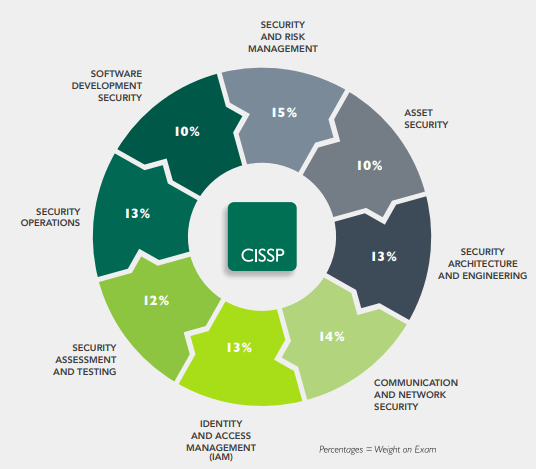
So, what does it take to earn the CISSP certificate? The CISSP exam is a four-hour Computerized Adaptive Test (CAT) of 125-175 questions to certify security professionals across eight domains:
- Security and Risk Management
- Asset Security
- Security Architecture and Engineering
- Communications and Network Security
- Identity and Access Management
- Security Assessment and Testing
- Security Operations
- Software Development Security
From access control and business continuity planning to cryptography, law and ethics, each domain references NIST standards. Since there are many cross-references and overlap between these domains, it can be confusing. Here’s a look at the CISSP NIST list of standards you should know for the CISSP exam.
NIST Standards for CISSP Exam
A multifaceted approach to solving cyber security issues is a critical skill tested in the CISSP exam. CISSPs should offer deep knowledge of issues such as architecture and access control to protect information system assets. To help clients and other stakeholders understand these issues, the security analyst must be able to assess current policies for incident response to recommend improvements. Likewise, security analysts must be able to compare and contrast cryptographic protocols to recommend ways to improve security. Creating an integrated, consistent system of policies, standards, and guidelines to protect an organization’s information and evaluate its risk is the end goal of a CISSP.
NIST standards were carefully created to guide federal agencies and their contractors. These standards become the north star for organizations striving to deliver secure solutions. While NIST provides many standards related to cybersecurity, the most relevant for the CISSP exam are the NIST SP 800 and the FIPS Series which include:
SP 800 Series
NIST SP 800-12: An Introduction to Information Security
NIST SP 800-30: Guide for Conducting Risk Assessments of Federal Information Systems and Organizations
NIST SP 800-34: Contingency Planning Guide for Federal Information Systems
NIST SP 800-37: Risk Management Framework for Information Systems and Organizations
NIST SP 800-53: Security and Privacy Controls for Federal Information Systems
NIST SP 800-53A: Assessing Security and Privacy Controls in Federal Information Systems and Organizations
NIST SP 800-60: Guide for Mapping Types of Information and Information Systems to Security Categories
NIST SP 800-63-3: Digital Identity Guidelines
NIST SP 800-88: Guidelines for Media Sanitization
NIST SP 800-126: The Technical Specification for the Security Content Automation Protocol (SCAP)
NIST SP 800-154: Guide to Data-centric System Threat Modelling
NIST SP 800-160: Systems Security Engineering
NIST SP 800-171: Protecting Controlled Unclassified Information in Non-federal Systems and Organizations
NIST SP 800-171A: Assessing Security Requirements for Controlled Unclassified Information
FIPS Series
FIPS 140-3: Security Requirements for Cryptographic Modules.
FIPS 199: Standards for Security Categorization of Federal Information and Information Systems.
FIPS 200: Minimum Security Requirements for Federal Information and Information Systems.

How to Become Certified as a CISSP
As a baseline to certification, you will need five or more years of full-time, paid work as a security analyst in at least two of eight domains covered in the CISSP. (Experience waivers are available for those with college degrees and additional credentials if approved by the ISC2.) A second option is to become an Associate of (ISC2) by passing the CISSP exam and earning the certification when you meet the experience requirement.
Next, you’ll need to prepare for and pass the exam which requires a minimum score of 700 out of 1,000 points.
Once you pass the CISSP exam, you will need certain endorsements – one to subscribe to the ISC2 Code of Ethics and one from another ISC2professional. This second endorsement should verify experience requirements ¬ these include length of employment, professional reputation, and continuing education as a security analyst.
Getting this endorsement points to the value of keeping memberships in professional memberships and attending seminars and events. With the right visibility and connections, you can network your way to people who will endorse your CISSP application.
Every year, an annual fee of $125 is required to maintain a CISSP certification. Every three years, you must either obtain 120 Continuing Professional Education (CPE) credits or retake the exam to remain a member in good standing. Within the three-year certification cycle, CISSPs can earn CPE credits by taking classes at a university or through online courses dedicated to security issues, training for additional certifications, reading information security related books, etc.
A professional who earns and keeps the title of CISSP can demonstrate technical knowledge and proficiency in these areas critical to an organization’s cyber security posture:
- CISSP analysts really know network architecture and design to implement the right network architecture to deter threats and leverage resources.
- CISSPs understand that the lifecycle effectiveness of software security applications is essential to smart, safe solutions
- CISSP analysts are able to both collect digital forensic evidence and maintain the integrity of the evidence they collect.
- Finally, CISSPs demonstrate knowledge of physical security systems and their value to network security systems.
In our work providing tailored, scalable solutions to government and industry, CISSPs are crucial assets for our team. It takes superior knowledge to stay ahead of cyber threats and help organizations protect their privacy. The right talent and expertise make all the difference. Become a CISSP to show the world your high standards.


